Ms.Janet Tran
Skype: janet.tran.92
WhatsApp: +84 963 296 509
Email: [email protected]
You can use this extension to interoperate with any Identity Provider, enabling SSO at the backend for administrators. It works with any IDP providers, including OneLogin, Okta, Ping Identity, ADFS, Salesforce, SharePoint,..

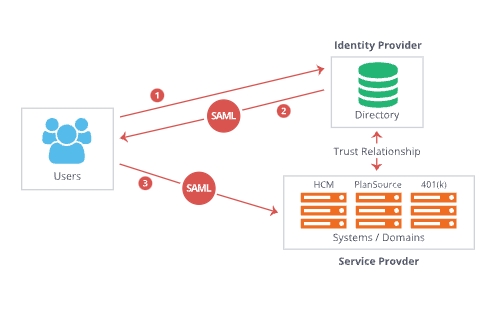
The extension add SAML support at Magento deploying a Service Provider. On this extension the SAML flow can be initiated at the Identity Provider or at the Service Provider. Once metadata info is exchange between the entities and the rest of the settings configured on the admin panel, the Single Sign On feature is available and a customized link will appear on the admin login form.

With this extended admin login form, your users can access Magento backend with any the Identity Provider established, they just click on the link “Login via your Identity Provider”, (the message is customizable) to carry out their login process.

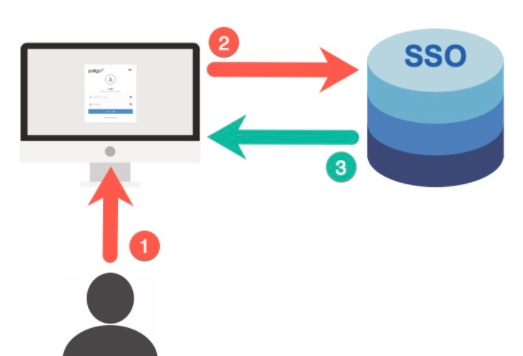
Magento 2 Single Sign On module streamlines local and remote application by providing simultaneous logins. Using this module, the user can enter the login credentials in the third-party application and be logged in to Magento 2 store simultaneously. This allows faster access to applications.

The customers can use their existing credentials for logging into various third-party applications such as OneLogin, Okta, Auth0, Auth0 Enterprise ADFS, Azure AD and Azure AD B2C, Keycloak, Salesforce... The user can use one set of credentials for various platforms and won’t have to remember multiple passwords for each login.

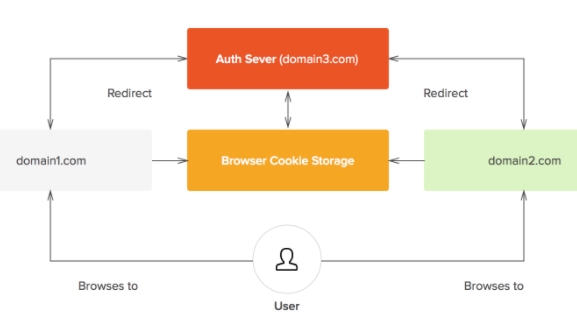
With Magento single sign-on users only have to enter one set of credentials to access their web apps in the cloud and behind the firewall – via desktops, smartphones and tablets. Secure single sign-on integration with Magento saves your organization time and money while significantly increasing the security of your data in the cloud.

The module was implemented by Sixto Martin, author of 15+ SAML plugins and several SAML toolkits. Companies like Cisco, Erickson, Philips, Royal Mail, Securitas, Mazda, Proclinic, Tendam, Woodmark, Toyota, Hilton, PWC, Deloitte; as well as Medical Associations, ONGs as well as Universities, trusted in the SAML extension.
Single Sign-on (SSO) is an authentication process that allows a user to access multiple applications with one set of login credentials. Similarly, the Magento 2 SSO module streamlines local and remote application by providing simultaneous logins.

Magento Single Sign-on extension will allow you to create and manage the unlimited number of integrations for both the Identity Provider and Service Provider modes. Just set up security details, test the connection and check the result on the frontend.

The admin may allow users to log in to third-party applications with their Magento credentials. The Magento 2 SSO module allows simultaneous logins via an option to enter the login credentials in the third-party application and be logged in to Magento 2 store simultaneously.
Security Access Markup Language (SAML) is an XML-based open standard that is used by web browsers to enable SSO. SAML can help you secure user logins and provide faster and more secure access to the applications. Our Magento 2 extension will support SAML.

Secure your Magento application from password theft using multi-factor authentication methods. To provide users with the highest level of security, this extension will support 2-factor authentication. It helps to keep the login safe even if the password is stolen.
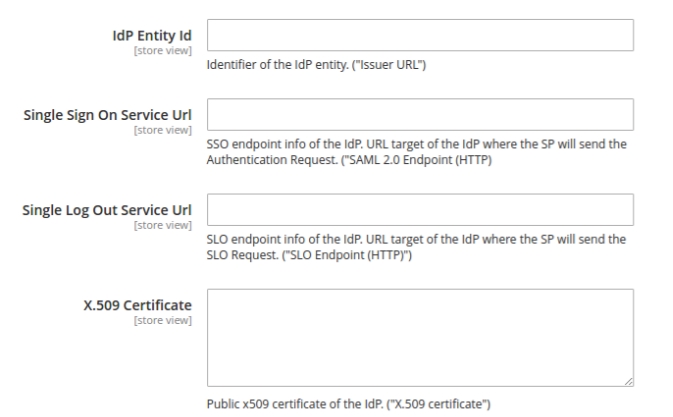
It is quite easy for the admin to add/delete/edit/view the SSO integrations. allows admin to specify an entity ID of a required identity provider, as well as URLs where authentication (SSO) and logout (SLO) requests should be sent.
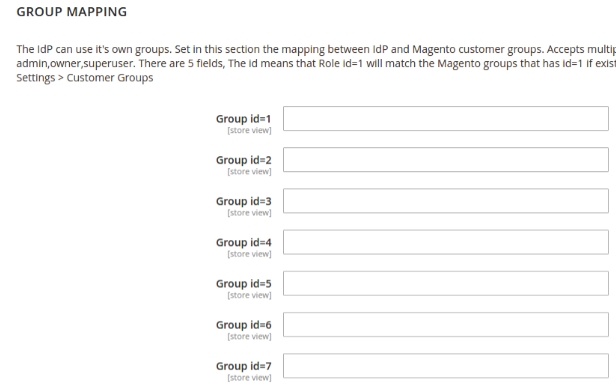
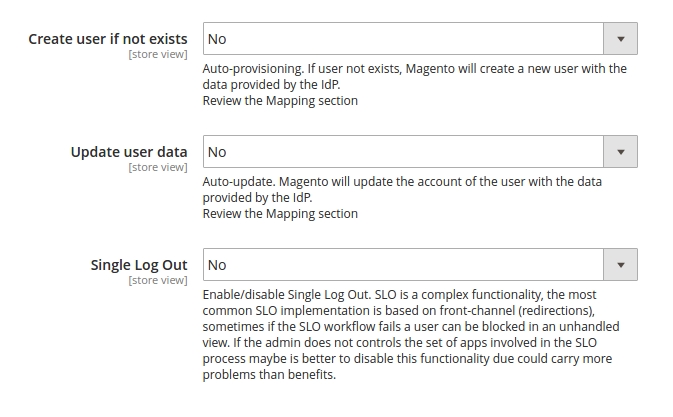
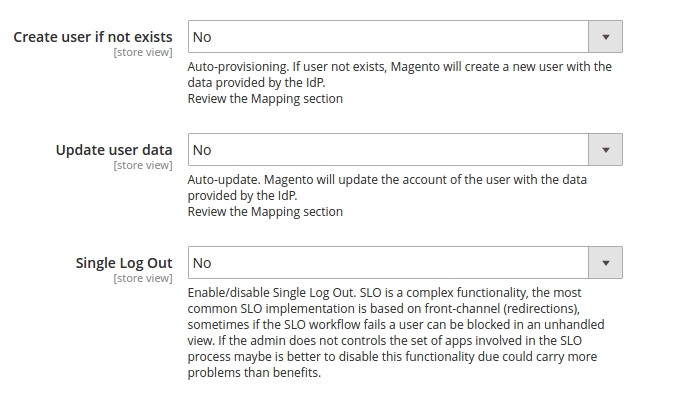
Newly created customers on Magento 2 store can be synchronized with the LDAP Server. Besides, the Magento 2 SSO module’s settings allow activating the feature that will force your storefront visitors to log in via IdP and enabling/disabling the Single Log Out option.
The following features will help you better understand our products
Bring you the shortest way to understand this product
You can find the best answers when you catch problems
IdP-initiated Single Sign-On
A SAMLRequest is sent to the Identity Provider, customer authenticates against the SAML Identity Provider and then information about the user, group and address are sent to Magento in a SAMLResponse, Magento SAML extension validates the SAMLResponse, authenticate customer (provisioning a new account if required and the feature is enabled) and let him in.
SP-initiated Single Sign-On
Like the previous scenario, but here the SAML Response is directly sent by the Identity Provider and processed by the Magento SAML extension.
SP-initiated Single Logout
A SAML Logout Request is sent to the Identity Provider, the IdP close its session and the session of other related Service Providers and sent back a Logout Response to the Magento instance that will close the session.
IdP-initiated Single Logout
A SAML Logout Request is sent by the Identity Provider, the Magento instance validates it, close its session and reply back a SAML Logout Response.
Find here a list of some of the Identity Providers supported. (Links refer to its official documentation to configure a SAML integration).
OneLogin
Okta
Auth0, Auth0 Enterprise
ADFS
Azure AD and Azure AD B2C
Keycloak
Salesforce
Shibboleth
simpleSAMLphp
AWS SSO
Centrify
Forgerock (OpenAM)
Ping Identity
RSA
IBM
Oracle
WSO2
NetIQ
SecureAuth
Citrix Netscaler
F5 BIG-IP
Use as License Key the Order ID of the purchase. When you purchase the extension, you can use it in one M2 instance. In the case of M2 running multi-sites, the license cover 3 stores using SAML SSO. If you require more stores, contact [email protected] to discuss the terms. Test and developer environments can use the extension without requiring an additional license.
Security Assertion Markup Language 2.0 (SAML 2.0) is a version of the SAML standard for exchanging authentication and authorization identities between security domains. SAML 2.0 is an XML-based protocol that uses security tokens containing assertions to pass information about a principal (usually an end user) between a SAML authority, named an Identity Provider, and a SAML consumer, named a Service Provider. SAML 2.0 enables web-based, cross-domain single sign-on (SSO), which helps reduce the administrative overhead of distributing multiple authentication tokens to the user.
SAML 2.0 was ratified as an OASIS Standard in March 2005, replacing SAML 1.1. The critical aspects of SAML 2.0 are covered in detail in the official documents SAMLCore,[1] SAMLBind,[2] SAMLProf,[3] and SAMLMeta.[4]
Some 30 individuals from more than 24 companies and organizations were involved in the creation of SAML 2.0. In particular, and of special note, Liberty Alliance donated its Identity Federation Framework (ID-FF) specification to OASIS, which became the basis of the SAML 2.0 specification. Thus SAML 2.0 represents the convergence of SAML 1.1, Liberty ID-FF 1.2, and Shibboleth 1.3.
SAML is a standard for exchanging authentication and authorization data between different domains.
Learn more here: https://en.wikipedia.org/wiki/SAML_2.0
Learn more at: https://github.com/jch/saml
Please fill out the customization request form if you need any
Recently, we discovered how client loving working with us by their 5 star recommedation





